
Enterprises across the globe are navigating a complex data paradox. Data is core to multiple organization-wide initiatives such as digital transformation, AI transformation, competitive differentiation and creating a niche value proposition. However, the accumulation of unprecedented volumes of data as part of these initiatives is, in itself, creating significant complexity. As organizations amass massive volumes of emails, files, backups, and application data, they simultaneously expand their exposure to regulatory scrutiny, cyber risk, and operational inefficiencies.
On the other hand, with the advent of an AI era, global regulations such as GDPR, CCPA, HIPAA, SEC Rule 17a-4, DPDP Act etc., are becoming extremely stringent. They not only demand the data to be handled in a secured manner, but also that the data should have a strict role-based access control and a well-defined retention period per the norms and regulations. This has propelled the idea of prioritizing precision, accountability and continuous governance rather than storing everything just for the sake of it, ultimately leading to the conception of the ideology of Data Minimization, the practice of collecting, processing, and retaining only the data necessary for a defined purpose, ensuring it remains relevant, limited, and accessible only for as long as required.
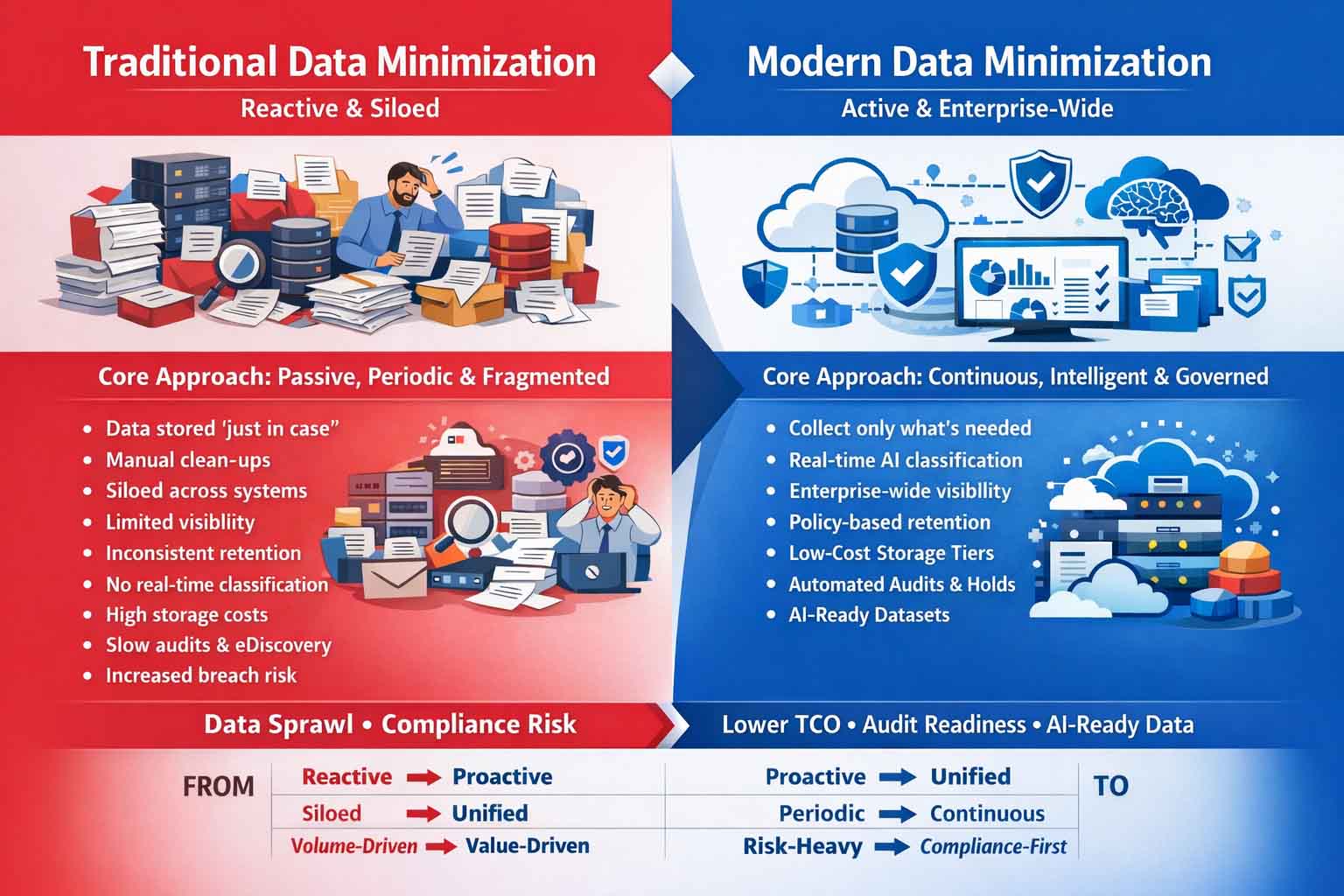
Fig. Traditional Data Minimization versus Modern Data Minimization
Redefining Data Minimization: Enterprise-wide and Active at Core
Modern enterprises are revamping the entire data minimization ecosystem by going beyond the classical definition of data minimization- collecting and storing data to only what’s necessary. Today data minimization should have a two-pronged approach; enterprise-wide in scope and active in execution.
An enterprise-wide approach ensures that minimization is not isolated to any system or department, rather it extends across formats and domains- structured and unstructured, on-prem and cloud, legacy and modern applications, creating a unified governance fabric- a single source of truth.
Active minimization, on the contrary, is a continuous and adaptive process. Traditional passive exercises involve static policies or periodic clean-up activities which is not feasible to the modern and dynamic data environments. However, active data minimization involves real-time monitoring, automated classifications, policy driven retentions, and defensible deletions- all aligned to the regulatory guidelines and strategic business objectives.

Fig. Enterprise-Wide and Active Minimization Strategy
The Regulatory Imperative: Why Minimization Cannot Be Passive
These days, regulatory frameworks are prescriptive mandates that require organizations to show control, accountability, and intent rather than just guidelines. There is very little room for doubt because these regulations are firmly rooted in concepts like purpose limitation, storage limitation, and the minimum threshold standard.
Over-retention becomes a liability rather than a protection in this situation. Retaining extraneous data broadens the scope of audits, increases the potential impact of breaches, and makes legal discovery procedures more difficult. Furthermore, regulators are putting more and more pressure on companies to explain not just why data is kept but also why it hasn’t been erased. This change emphasises the need for an active and auditable approach to data minimisation by placing defendable deletion at the core of compliance strategies.
Excessive Data: The Cost Implications
The financial and operational implications of excessive data are detrimental to any organization. Storage costs rise significantly because an organization retains unprecedented amounts of obsolete and redundant data in premium storage tiers. Business Continuity Management (BCM) processes become increasingly complex and expensive, and e-Discovery processes expand in turn. On top of this, there’s an additional expense in terms of cybersecurity risk. An add-on dataset provides an additional entry point for attackers, increasing the likelihood of a breach. Generative AI and LLMs rely on high-quality datasets. If the datasets are uncurated, inaccurate and biased, the resulting output would be non-compliant. In this sense, data minimization is not just about reducing the overall volume, but about enhancing value.
Data Minimization as a Strategic Lever
Cost Savings
Embracing data minimization cuts expenses on storage, infrastructure, and operations by eliminating redundant and obsolete data.
Improved Compliance
Organizations respond faster and more precisely to audits and legal requests, shifting from reactive to proactive processes.
Reduced Cybersecurity Risks
A minimized data environment with fewer assets and tighter access controls strengthens security and resilience against threats.
Foundation for AI Innovation
Clean, structured datasets power accurate analytics, effective ML models, and reliable decision-making, thereby, paving the way for a faster analytics governance procedure.
Growth Catalyst
Data minimization transforms from a constraint into an enabler for innovation and business growth
Case Study: Top-30 BFSI Major Implements an Enterprise-wide Data Minimization Strategy
| Challenges | Solution Approach | Benefits |
|---|---|---|
| 25-30% YoY data growth | Enterprise-wide data discovery | Significant increase in operational efficiency |
| 60-70% inactive data | Intelligent classification and tagging | Reduction in costs by upto 50% |
| Disparate systems with data siloes | Policy-based archiving and tiering | 100% adherence to compliance norms and guidelines |
| Compliance risks | Defensible deletion framework | AI readiness with curated, high-quality datasets for faster AI/ML implementation |
| Inefficient e-Discovery cycles | Unified governance and auditability | Reduced data exposure and breach risks |
Conclusion
Organizations today stand at a pivotal point- not in how much data they can hoard, but in how intelligently they manage what they retain. Amid intensifying regulatory pressures, soaring infrastructure costs, and escalating breach risks, indiscriminate data accumulation has become untenable. True competitive edge emerges from pivoting to active, policy-driven governance. By embedding data minimization as an enterprise-wide discipline- continuously enforced through classification, retention policies, and defensible deletion- organizations balance control with agility. Every byte retained must justify its place via clear regulatory, operational, or strategic value, with ownership and accountability woven into daily workflows. Pioneers in this shift slash risks, cut costs, accelerate audits, fortify compliance, and build a resilient data foundation- primed to dominate the era of data-driven innovation.
DISCLAIMER: THE CONTENT, VIEWS, AND OPINIONS EXPRESSED IN THIS BLOG ARE SOLELY THOSE OF THE AUTHOR(S) AND DO NOT REFLECT THE OFFICIAL POLICY OR POSITION OF SOLIX TECHNOLOGIES, INC., ITS AFFILIATES, OR PARTNERS. THIS BLOG IS OPERATED INDEPENDENTLY AND IS NOT REVIEWED OR ENDORSED BY SOLIX TECHNOLOGIES, INC. IN AN OFFICIAL CAPACITY. ALL THIRD-PARTY TRADEMARKS, LOGOS, AND COPYRIGHTED MATERIALS REFERENCED HEREIN ARE THE PROPERTY OF THEIR RESPECTIVE OWNERS. ANY USE IS STRICTLY FOR IDENTIFICATION, COMMENTARY, OR EDUCATIONAL PURPOSES UNDER THE DOCTRINE OF FAIR USE (U.S. COPYRIGHT ACT § 107 AND INTERNATIONAL EQUIVALENTS). NO SPONSORSHIP, ENDORSEMENT, OR AFFILIATION WITH SOLIX TECHNOLOGIES, INC. IS IMPLIED. CONTENT IS PROVIDED "AS-IS" WITHOUT WARRANTIES OF ACCURACY, COMPLETENESS, OR FITNESS FOR ANY PURPOSE. SOLIX TECHNOLOGIES, INC. DISCLAIMS ALL LIABILITY FOR ACTIONS TAKEN BASED ON THIS MATERIAL. READERS ASSUME FULL RESPONSIBILITY FOR THEIR USE OF THIS INFORMATION. SOLIX RESPECTS INTELLECTUAL PROPERTY RIGHTS. TO SUBMIT A DMCA TAKEDOWN REQUEST, EMAIL INFO@SOLIX.COM WITH: (1) IDENTIFICATION OF THE WORK, (2) THE INFRINGING MATERIAL’S URL, (3) YOUR CONTACT DETAILS, AND (4) A STATEMENT OF GOOD FAITH. VALID CLAIMS WILL RECEIVE PROMPT ATTENTION. BY ACCESSING THIS BLOG, YOU AGREE TO THIS DISCLAIMER AND OUR TERMS OF USE. THIS AGREEMENT IS GOVERNED BY THE LAWS OF CALIFORNIA.
-
 White Paper
White PaperEnterprise Information Architecture for Gen AI and Machine Learning
Download White Paper -

-

-

